| A new report from Trustwave cybersecurity researchers SpiderLabs has claimed hackers are increasingly turning to the Greatness phishing kit due to its advanced features, simplicity in use, and relatively low cost. |  |
New Jersey School District Shut Down by Cyberattack
 |
Sunday night, Freehold Township district officials notified its staff and parents that school would not be in session Monday due to technical difficulties caused by a cyber incident. |
Protecting Critical Infrastructure Means Getting Back to Basics
| Critical infrastructure organizations need to recognize that the technology and cybersecurity landscapes have changed. |  |
ChatGPT Quip &
|
 |
|
There once was an Association Head of IT, |
FTC bans data broker from selling Americans’ location data
| Today, the U.S. Federal Trade Commission (FTC) banned data broker Outlogic, formerly X-Mode Social, from selling Americans’ raw location data that could be used for tracking purposes. |  |
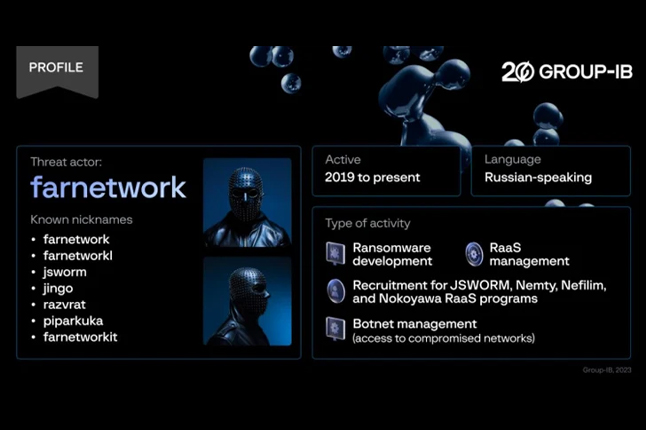
There is a Ransomware Armageddon Coming for Us All
 |
Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop |
Applying the Tyson Principle to Cybersecurity: Why Attack Simulation is Key to Avoiding a KO
| Picture a cybersecurity landscape where defenses are impenetrable, and threats are nothing more than mere disturbances deflected by a strong shield. Sadly, this image of fortitude remains a pipe dream despite its comforting nature.evolving nature of Large Language Models, but the evolving ways in which they can be attacked and defended. We’re going to talk in this article about four items in that top 10 that are most able to contribute to the accidental disclosure of secrets such as passwords, API keys, and more. |  |
Threat Actors Increasingly Abusing GitHub for Malicious Purposes
 |
The ubiquity of GitHub in information technology (IT) environments has made it a lucrative choice for threat actors to host and deliver malicious payloads and act as dead drop resolvers, command-and-control, and data exfiltration points. |
SEC X Account Hack Draws Senate Outrage
| Senators from both parties called the Securities and Exchange Commission’s lack of MFA “inexcusable” and demand investigation into the regulator’s cybersecurity lapse. |  |
Vulnerability Vortex
Critical Cisco Unified Communications RCE Bug Allows Root Access
| The vulnerability, tracked as CVE-2024-20253, makes enterprise communications infrastructure and customer service call centers sitting ducks for unauthenticated cyberattackers. |  |
Google Warns of Chrome Browser Zero-Day Being Exploited
 |
The exploited zero-day, tagged as CVE-2024-0519, is described as an out-of-bounds memory access issue in the V8 JavaScript engine. |
Alert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now
| Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be potentially exploited to cause a denial-of-service (DoS) condition and remote code execution (RCE). | 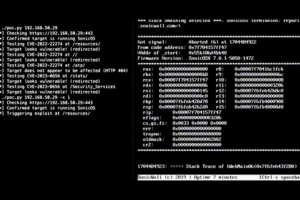 |
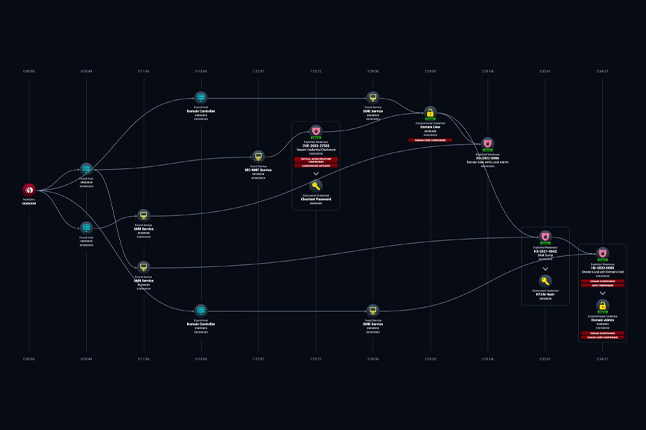
Ransomware Actor Uses TeamViewer to Gain Initial Access to Networks
 |
Attackers have increasingly leveraged the widely used remote access tool, installed on hundreds of millions of endpoints, to break into victim environments. |
Read also

Welcome to v062 : Roses are red, violets are blue, cyber-hackers are waiting for you

Welcome to v061 : New Year’s Resolution: Strengthen Cybersecurity, Protect Missions.
About Us

Developing cybersecurity plans, evaluating and implementing technology, building effective software, and executing strategic initiatives.