Breach: TicketMaster Confirms Data Breach Impacting 560 Million Customers
| Ticketmaster owner Live Nation confirmed the Ticketmaster data breach that compromised the data of 560 million customers. |  |
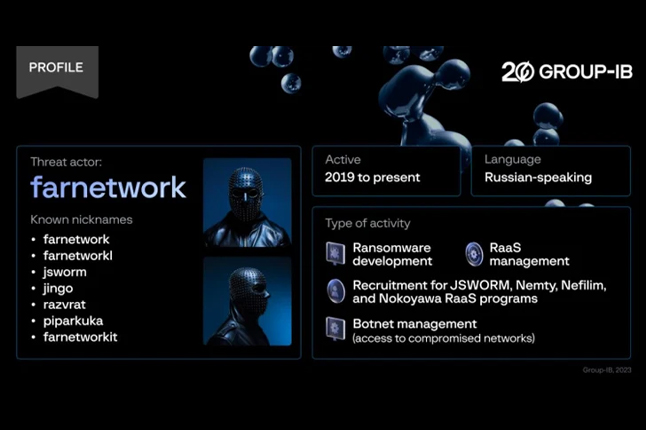
News: Rebranded Knight Ransomware Targeting Healthcare and Businesses Worldwide
 |
An analysis of a nascent ransomware strain called RansomHub has revealed it to be an updated and rebranded version of Knight ransomware, itself an evolution of another ransomware known as Cyclops. |
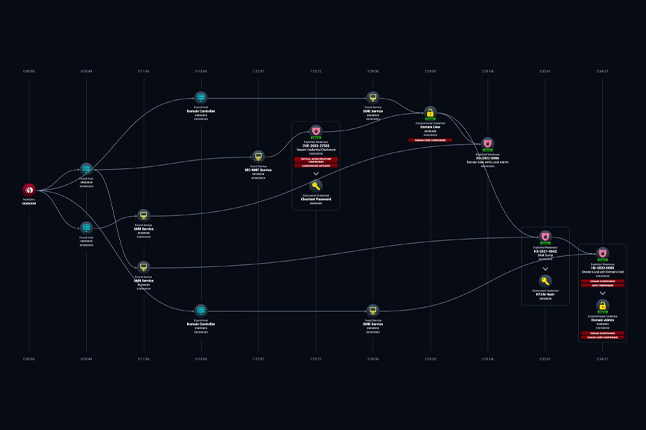
Protection: How to Detect and Respond to the Surge in Cloud-Based Token Theft
| This year, there has been a spate of cloud-based token theft. These tokens are issued by identity and access management services such as Azure Active Directory (AD), and they contain sensitive information like usernames, source IP addresses, MFA, and corporate account permissions. These tokens are the backbone of how your employees access company resources – both in the office and at home. And they are growing increasingly vulnerable to two types of exploitative techniques: adversary-in-the-middle (AitM) and pass-the-cookie attacks. |  |
Cyber Savvy AI Antics |
 |
|
Can you figure out this song? A long, long time ago, when spam was just a trickle, So bye-bye to your data supply,
|
News: Third-Party Cyber Attacks: The Threat No One Sees Coming – Here’s How to Stop Them
| Learn about critical threats that can impact your organization and the bad actors behind them from Cybersixgill’s threat experts. Each story shines a light on underground activities, the threat actors involved, and why you should care, along with what you can do to mitigate risk. |  |
News: Prevent Account Takeover with Better Password Security
 |
Tom works for a reputable financial institution. He has a long, complex password that would be near-impossible to guess. He’s memorized it by heart, so he started using it for his social media accounts and on his personal devices too. Unbeknownst to Tom, one of these sites has had its password database compromised by hackers and put it up for sale on the dark web. Now threat actors are working hard to link these leaked credentials back to real-life individuals and their places of work. Before long, a threat actor will use Tom’s legitimate email account to send a spear-phishing link to his CEO. |
AI: The AI Debate: Google’s Guidelines, Meta’s GDPR Dispute, Microsoft’s Recall Backlash
| Google is urging third-party Android app developers to incorporate generative artificial intelligence (GenAI) features in a responsible manner. |  |
News: FBI Kicks Hackers In The Teeth With Free 7,000 Ransomware Key Giveaway
 |
The FBI is encouraging anyone who has been a victim of the LockBit ransomware group and its many affiliates to contact them for a free decryption key that could help restore their data. Bryan Vorndran, FBI Cyber Division assistant director, has urged potential victims to contact the Bureau after confirming that it is in possession of more than 7,000 decryption keys from the ransomware hackers. |
News: Cybercriminals Exploit CrowdStrike Update Mishap to Distribute Remcos RAT Malware
| Cybersecurity firm CrowdStrike, which is facing the heat for causing worldwide IT disruptions by pushing out a flawed update to Windows devices, is now warning that threat actors are exploiting the situation to distribute Remcos RAT to its customers in Latin America under the guise of providing a hotfix. |  |
News: US Cybercrime and Cybersecurity Statistics (Updated 2023)
 |
Cybercrime in the United States is becoming a concern to individuals and organizations alike. As a result of this current trend, companies across the United States are faced with ransomware attacks, phishing schemes, and fraud. Cybercrime costs will hit $8 trillion in 2023 and reach $10.5 trillion by 2025. |
App Testing: 6 Types of Applications Security Testing You Must Know About
| Application security testing is a critical component of modern software development, ensuring that applications are robust and resilient against malicious attacks. As cyber threats continue to evolve in complexity and frequency, the need to integrate comprehensive security measures throughout the SDLC has never been more essential. Traditional pentesting provides a crucial snapshot of an application’s security posture, but when integrated across the SDLC, it allows for early detection and mitigation of vulnerabilities, reducing the risk of costly post-deployment fixes and enhancing overall security. |  |
News: New Chrome Feature Scans Password-Protected Files for Malicious Content
 |
Google said it’s adding new security warnings when downloading potentially suspicious and malicious files via its Chrome web browser. |
Cybercrime: This AI-Powered Cybercrime Service Bundles Phishing Kits with Malicious Android Apps
| A Spanish-speaking cybercrime group named GXC Team has been observed bundling phishing kits with malicious Android applications, taking malware-as-a-service (MaaS) offerings to the next level. |  |
News: A Bug in Chrome Password Manager Caused User Credentials to Disappear
 |
Google addressed a Chrome’s Password Manager bug that caused user credentials to disappear temporarily for more than 18 hours. |
News: CrowdStrike Outage Losses Estimated at a Staggering $5.4B
| Researchers track the healthcare sector as experiencing the biggest financial losses, with banking and transportation following close behind. |  |
News: July Windows Server updates break Remote Desktop connections
 |
Microsoft has confirmed that July’s security updates break remote desktop connections in organizations where Windows servers are configured to use the legacy RPC over HTTP protocol in the Remote Desktop Gateway. |
Vulnerability Vortex
Google Patches New Android Kernel Vulnerability Exploited in the Wild
| Google has addressed a high-severity security flaw impacting the Android kernel that it said has been actively exploited in the wild. |  |
Windows Downgrade Attack Risks Exposing Patched Systems to Old Vulnerabilities
 |
Microsoft said it is developing security updates to address two loopholes that it said could be abused to stage downgrade attacks against the Windows update architecture and replace current versions of the operating system files with older versions. |
Chrome, Firefox Updates Patch Serious Vulnerabilities
| A Chrome 127 update patches five vulnerabilities, and Firefox 129 addresses over a dozen security holes. |  |
0.0.0.0 Day: 18-Year-Old Browser Vulnerability Impacts MacOS and Linux Devices
 |
Cybersecurity researchers have discovered a new “0.0.0.0 Day” impacting all major web browsers that malicious websites could take advantage of to breach local networks. |
Microsoft Warns of Unpatched Office Vulnerability Leading to Data Exposure
| Microsoft has disclosed an unpatched zero-day in Office that, if successfully exploited, could result in unauthorized disclosure of sensitive information to malicious actors. |  |
Microsoft Issues Patches for 90 Flaws, Including 10 Critical Zero-Days
 |
Microsoft on Tuesday shipped fixes to address a total of 90 security flaws, including 10 zero-days, of which six have come under active exploitation in the wild. |
Microsoft Found OpenVPN Bugs That Can Be Chained to Achieve RCE and LPE
| Microsoft found four bugs in OpenVPN that could be chained to achieve remote code execution and local privilege escalation. |  |
Fortinet, Zoom Patch Multiple Vulnerabilities
 |
Patches announced on Tuesday by Fortinet and Zoom address multiple vulnerabilities, including high-severity flaws leading to information disclosure and privilege escalation in Zoom products. |
Adobe Releases Security Updates for Multiple Products
| Adobe released security updates to address multiple vulnerabilities in Adobe software. A cyber threat actor could exploit some of these vulnerabilities to take control of an affected system. |  |
New Banshee Stealer Targets 100+ Browser Extensions on Apple macOS Systems
 |
Cybersecurity researchers have uncovered new stealer malware that’s designed to specifically target Apple macOS systems. |
Read also

Welcome to v062 : Roses are red, violets are blue, cyber-hackers are waiting for you

Welcome to v061 : New Year’s Resolution: Strengthen Cybersecurity, Protect Missions.
About Us

Developing cybersecurity plans, evaluating and implementing technology, building effective software, and executing strategic initiatives.