News: Hazy Issue in Entra ID Allows Privileged Users to Become Global Admins
| Invisible authentication mechanisms in Microsoft allow any attacker to escalate from privileged to super-duper privileged in cloud environments, paving the way for complete takeover. |  |
News: Sonos Speaker Flaws Could Have Let Remote Hackers Eavesdrop on Users
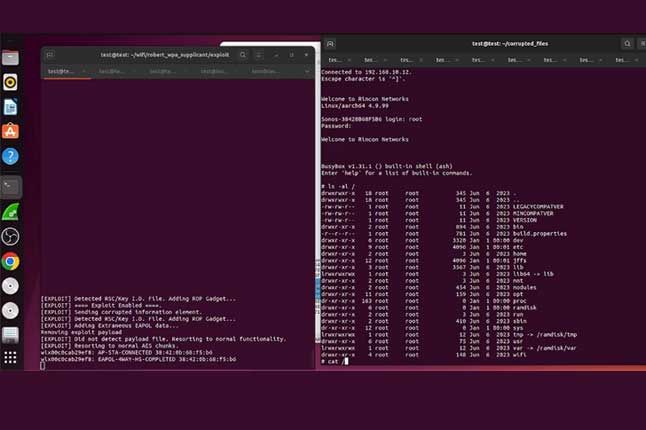 |
Cybersecurity researchers have uncovered weaknesses in Sonos smart speakers that could be exploited by malicious actors to clandestinely eavesdrop on users. |
News: How Phishing Attacks Adapt Quickly to Capitalize on Current Events
| In 2023, no fewer than 94 percent of businesses were impacted by phishing attacks, a 40 percent increase compared to the previous year, according to research from Egress. |  |
Cyber Savvy AI Antics |
 |
|
Give 5 options for finishing a joke that starts….”How many security engineers does it take to tell you the time?” 1. “None, they’ll just tell you it’s a security risk to know.” 2. “One, but they’ll encrypt the answer and make you decrypt it yourself.” 3. “It depends—did you remember to patch the clock?” 4. “Just one, but first they’ll have to run a vulnerability scan on the clock.” 5. “As many as it takes to write a report explaining why they can’t tell you.” |
AI: The AI Hangover is Here – The End of the Beginning
| After a good year of sustained exuberance, the hangover is finally here. It’s a gentle one (for now), as the market corrects the share price of the major players (like Nvidia, Microsoft, and Google), while other players reassess the market and adjust priorities. Gartner calls it the trough of disillusionment, when interest wanes and implementations fail to deliver the promised breakthroughs. Producers of the technology shake out or fail. Investment continues only if the surviving providers improve their products to the satisfaction of early adopters. |  |
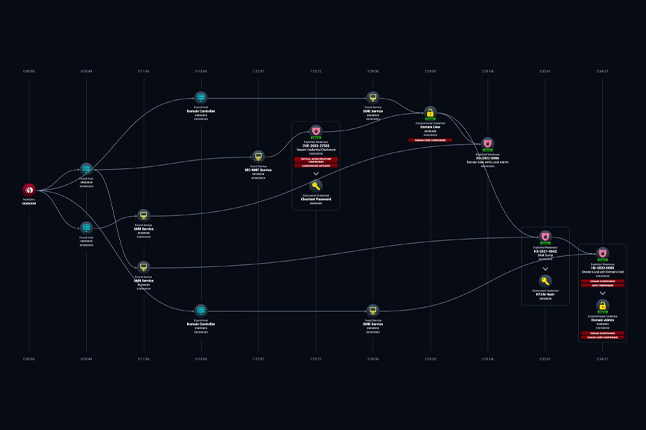
News: Hackers’ Toolkit Exposed, Wide Range of Tools from Initial Access to Full Control
 |
Cybersecurity researchers have discovered an extensive hacker toolkit, revealing a comprehensive set of tools designed for various stages of cyberattacks. |
News: DDoS Attacks Surge 46% in First Half of 2024, Gcore Report Reveals
| Monitoring evolving DDoS trends is essential for anticipating threats and adapting defensive strategies. The comprehensive Gcore Radar Report for the first half of 2024 provides detailed insights into DDoS attack data, showcasing changes in attack patterns and the broader landscape of cyber threats. Here, we share a selection of findings from the full report. |  |
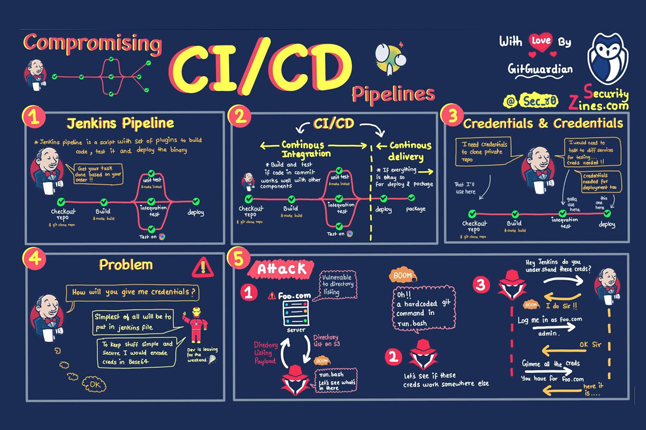
News: Identity Threat Detection and Response Solution Guide
 |
Identity Threat Detection and Response (ITDR) has emerged as a critical component to effectively detect and respond to identity-based attacks. Threat actors have shown their ability to compromise the identity infrastructure and move laterally into IaaS, Saas, PaaS and CI/CD environments. Identity Threat Detection and Response solutions help organizations better detect suspicious or malicious activity in their environment. ITDR solutions give security teams the ability to help teams answer the question “What’s happening right now in my environment – what are my identities doing in my environments.” |
Incident: Hackers may have stolen your Social Security number in a massive breach. Here’s what to know.
| A new lawsuit is claiming hackers have gained access to the personal information of “billions of individuals,” including their Social Security numbers, current and past addresses and the names of siblings and parents — personal data that could allow fraudsters to infiltrate financial accounts or take out loans in their names. |  |
News: Microsoft Issues Mandatory 2FA Login Deadline Alert
 |
Microsoft’s public cloud computing platform, Azure, was recently targeted by a cyberattack that led to a multi-hour outage. While a newly announced mandatory two-factor authentication login requirement would not have prevented that kind of distributed denial of service attack, it will have a positive impact when it comes to protecting user data and identity. |
News: Why you should be worried about massive National Public Data breach and what to do.
| The latest data breach uncovered is potentially one of the biggest ever, including 2.9 billion records on millions of Americans. Now many are considering freezing their credit reports. Why? |  |
Breach: Hackers Just Leaked a Bunch of Social Security Numbers. Here’s What To Know
 |
On April 8, 2024, a group of hackers known as “USDoD” posted to a hacking forum claims that they had access to over 2.9 billion records stolen from a background checking company known as National Public Data. According to the post, the data contained names, addresses and social security numbers of people located in the U.S. The group wanted to sell the data for $3.5 million. |
| In today’s rapidly evolving cyber threat landscape, organizations face increasingly sophisticated attacks targeting their applications. Understanding these threats and the technologies designed to combat them is crucial. This article delves into the mechanics of a common application attack, using the infamous Log4Shell vulnerability as an example, and demonstrates how Application Detection and Response (ADR) technology effectively safeguards against such zero-day threats. |  |
Cloud: Detecting AWS Account Compromise: Key Indicators in CloudTrail Logs for Stolen API Keys
 |
As cloud infrastructure becomes the backbone of modern enterprises, ensuring the security of these environments is paramount. With AWS (Amazon Web Services) still being the dominant cloud it is important for any security professional to know where to look for signs of compromise. |
Cybercrime: Ransomware rakes in record-breaking $450 million in first half of 2024
| Ransomware victims have paid $459,800,000 to cybercriminals in the first half of 2024, setting the stage for a new record this year if ransom payments continue at this level. |  |
News: Human Nature Is Causing Our Cybersecurity Problem
 |
By moving beyond guidelines and enforcing accountability, encouraging innovation, and prioritizing the safety and well-being of our communities in the digital age, we can build a more secure software future. |
Vulnerability Vortex
Chrome 128 Updates Patch High-Severity Vulnerabilities
| Google has released two Chrome 128 updates to address six high-severity vulnerabilities reported by external researchers. |  |
VMWare releases Fusion vulnerability with 8.8 rating
 |
The company issued a patch for the high-severity bug that allows arbitrary code execution. |
Critical Security Flaw Found in LiteSpeed Cache Plugin for WordPress
| Cybersecurity researchers have discovered yet another critical security flaw in the LiteSpeed Cache plugin for WordPress that could allow unauthenticated users to take control of arbitrary accounts. |  |
Veeam Releases Security Updates to Fix 18 Flaws, Including 5 Critical Issues
 |
Veeam has shipped security updates to address a total of 18 security flaws impacting its software products, including five critical vulnerabilities that could result in remote code execution. |
Sonicwall Warns That Sonicos Bug Exploited In Attacks
| Recently fixed access control SonicOS vulnerability, tracked as CVE-2024-40766, is potentially exploited in attacks in the wild, SonicWall warns. |  |
Microsoft Issues Patches for 79 Flaws, Including 3 Actively Exploited Windows Flaws
 |
Microsoft on Tuesday disclosed that three new security flaws impacting the Windows platform have come under active exploitation as part of its Patch Tuesday update for September 2024. |
Adobe Patches Critical, Code Execution Flaws in Multiple Products
| Patch Tuesday: Adobe releases patches for 28 security vulnerabilities and warned of code execution risks on Windows and macOS platforms. |  |
Ivanti fixes maximum severity RCE bug in Endpoint Management software
 |
Ivanti has fixed a maximum severity vulnerability in its Endpoint Management software (EPM) that can let unauthenticated attackers gain remote code execution on the core server. |
Read also

Welcome to v062 : Roses are red, violets are blue, cyber-hackers are waiting for you

Welcome to v061 : New Year’s Resolution: Strengthen Cybersecurity, Protect Missions.
About Us

Developing cybersecurity plans, evaluating and implementing technology, building effective software, and executing strategic initiatives.