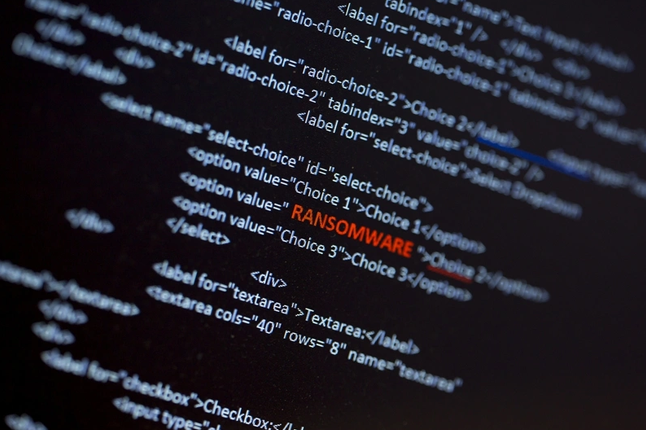
Ransomware: 2024 Breaks Records With Highest Ever Ransomware Attacks
 |
With a staggering 5263 attacks, 2024 saw the highest volume of ransomware attacks observed since 2021, according to a new report from cybersecurity consulting firm, NCC Group. |
News: Hackers Exploit Google Tag Manager to Deploy Credit Card Skimmers on Magento Stores
 |
Threat actors have been observed leveraging Google Tag Manager (GTM) to deliver credit card skimmer malware targeting Magento-based e-commerce websites. |
Attack: Cyberattack disrupts Lee newspapers’ operations across the US
 |
Lee Enterprises, one of the largest newspaper groups in the United States, says a cyberattack that hit its systems caused an outage last week and impacted its operations. |
Cyber Savvy AI Antics |
 |
| THIS. IS. MARCH CYBER MADNESS🏀🛡️
Sixty-four threats. One champion. Ransomware’s the top seed, but don’t sleep on Phishing U—they’ve got a killer social engineering game. Meanwhile, Zero-Day State just blew past Endpoint Tech with a full-court exploit! Will Firewalls hold the perimeter? Can MFA Tech stop the brute force fast break? And who *really* runs the dark web zone defense? Get ready for backdoor buzzer-beaters, cross-site scripting crossovers, and insider threat inbounds. March Madness: Cyber Bracket Edition – Where the only thing getting dunked… is your password. |
AI: How to Steer AI Adoption: A CISO Guide
 |
CISOs are finding themselves more involved in AI teams, often leading the cross-functional effort and AI strategy. But there aren’t many resources to guide them on what their role should look like or what they should bring to these meetings. |
Attack: North Korean Hackers Exploit PowerShell Trick to Hijack Devices in New Cyberattack
 |
The North Korea-linked threat actor known as Kimsuky has been observed using a new tactic that involves deceiving targets into running PowerShell as an administrator and then instructing them to paste and run malicious code provided by them. |
News: 4 Ways to Keep MFA From Becoming too Much of a Good Thing
 |
Multi-factor authentication (MFA) has quickly become the standard for securing business accounts. Once a niche security measure, adoption is on the rise across industries. But while it’s undeniably effective at keeping bad actors out, the implementation of MFA solutions can be a tangled mess of competing designs and ideas. For businesses and employees, the reality is that MFA sometimes feels like too much of a good thing. |
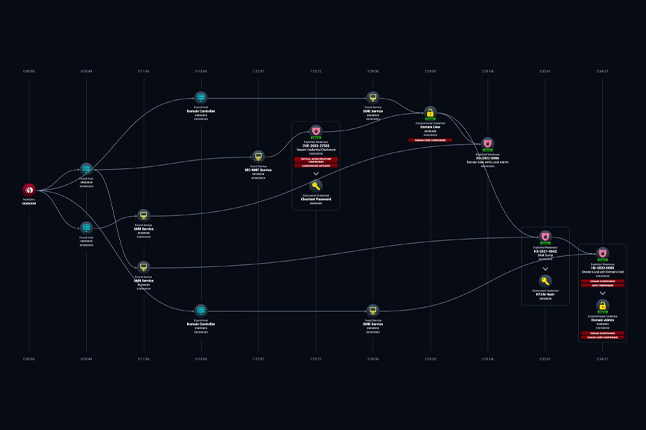
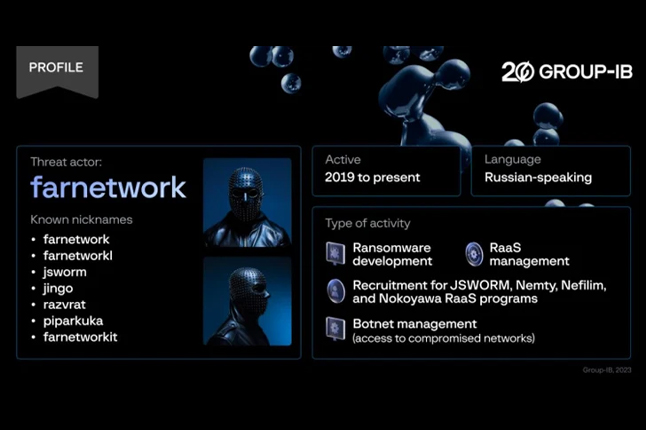
Crime: RansomHub Becomes 2024’s Top Ransomware Group, Hitting 600+ Organizations Globally
 |
The threat actors behind the RansomHub ransomware-as-a-service (RaaS) scheme have been observed leveraging now-patched security flaws in Microsoft Active Directory and the Netlogon protocol to escalate privileges and gain unauthorized access to a victim network’s domain controller as part of their post-compromise strategy. |
News: Hackers Use CAPTCHA Trick on Webflow CDN PDFs to Bypass Security Scanners
 |
A widespread phishing campaign has been observed leveraging bogus PDF documents hosted on the Webflow content delivery network (CDN) with an aim to steal credit card information and commit financial fraud. |
AI: AI-Powered Social Engineering: Ancillary Tools and Techniques
 |
Social engineering is advancing fast, at the speed of generative AI. This is offering bad actors multiple new tools and techniques for researching, scoping, and exploiting organizations. In a recent communication, the FBI pointed out: ‘As technology continues to evolve, so do cybercriminals’ tactics.’ |
AI: Google Chrome’s AI-powered security feature rolls out to everyone
 |
Google Chrome has updated the existing “Enhanced protection” feature with AI to offer “real-time” protection against dangerous websites, downloads and extensions. |
AI: Debunking the AI Hype: Inside Real Hacker Tactics
 |
Is AI really reshaping the cyber threat landscape, or is the constant drumbeat of hype drowning out actual, more tangible, real-world dangers? According to Picus Labs’ Red Report 2025 which analyzed over one million malware samples, there’s been no significant surge, so far, in AI-driven attacks. Yes, adversaries are definitely continuing to innovate, and while AI will certainly start playing a larger and larger role, the latest data suggests that a set of well-known tactics, techniques, and procedures (TTPs) are still dominating the field. |
News: Chase will soon block Zelle payments to sellers on social media
 |
JPMorgan Chase Bank (Chase) will soon start blocking Zelle payments to social media contacts to combat a significant rise in online scams utilizing the service for fraud. |
News: PCI DSS 4.0 Mandates DMARC By 31st March 2025
 |
The payment card industry has set a critical deadline for businesses handling cardholder data or processing payments- by March 31, 2025, DMARC implementation will be mandatory! This requirement highlights the importance of preventative measures against email fraud, domain spoofing, and phishing in the financial space. This is not an optional requirement as non-compliance may result in monetary penalties ranging from $5,000 to $100,000. Organizations can sign up for a DMARC analyzer trial to stay ahead of PCI DSS 4.0 requirements today! |
News: Phishing attack hides JavaScript using invisible Unicode trick
 |
A new JavaScript obfuscation method utilizing invisible Unicode characters to represent binary values is being actively abused in phishing attacks targeting affiliates of an American political action committee (PAC). |
AI: AI-Powered Deception is a Menace to Our Societies
 |
Wherever there’s been conflict in the world, propaganda has never been far away. Travel back in time to 515 BC and read the Behistun Inscription, an autobiography by Persian King Darius that discusses his rise to power. More recently, see how different newspapers report on wars, where it’s said, ‘The first casualty is the truth.’ |
Vulnerability Vortex
U.S. CISA Adds Fortinet Fortios/Fortiproxy and Github Action Flaws to its Known Exploited Vulnerabilities Catalog
 |
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Fortinet FortiOS/FortiProxy and GitHub Action flaws to its Known Exploited Vulnerabilities catalog. |
Malware campaign ‘DollyWay’ breached 20,000 WordPress sites
 |
A malware operation dubbed ‘DollyWay’ has been underway since 2016, compromising over 20,000 WordPress sites globally to redirect users to malicious sites. |
Zero-Day Alert: Google Releases Chrome Patch for Exploit Used in Russian Espionage Attacks
 |
Google has released out-of-band fixes to address a high-severity security flaw in its Chrome browser for Windows that has been exploited in the wild as part of attacks targeting organizations in Russia. |
Mozilla Patches Critical Firefox Bug Similar to Chrome’s Recent Zero-Day Vulnerability
 |
Mozilla has released updates to address a critical security flaw impacting its Firefox browser for Windows, merely days after Google patched a similar flaw in Chrome that came under active exploitation as a zero-day. |
Mozilla Fixed Critical Firefox Vulnerability CVE-2025-2857
 |
Mozilla addressed a critical vulnerability, tracked as CVE-2025-2857, impacting its Firefox browser for Windows. |
Splunk Patches Dozens of Vulnerabilities
 |
Splunk patches high-severity remote code execution and information disclosure flaws in Splunk Enterprise and Secure Gateway App. |
Read also

Welcome to v062 : Roses are red, violets are blue, cyber-hackers are waiting for you

Welcome to v061 : New Year’s Resolution: Strengthen Cybersecurity, Protect Missions.
About Us

Developing cybersecurity plans, evaluating and implementing technology, building effective software, and executing strategic initiatives.